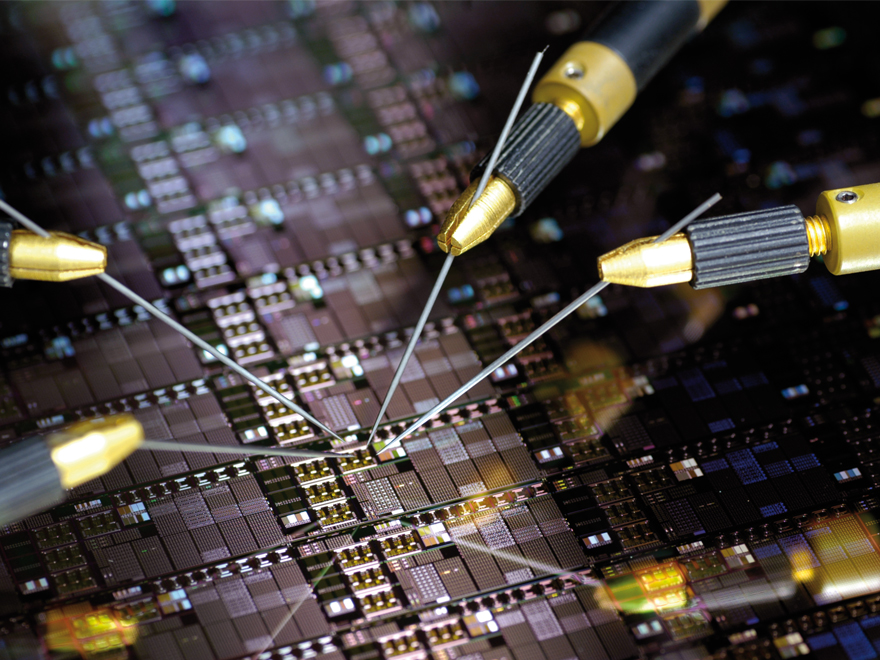
The subjects of functional safety and cyber security play an increasingly big role in the specification and the design of the modern integrated circuits. These circuits include a specialized analog part and customer-specific interfaces and often also an embedded processor core.
Especially in the selection of the processors that are to be integrated, a suitable architecture is needed that guarantees to fulfill the requirements of functional safety and is robust against cyber attacks.
Fraunhofer IMS offers secured processor cores on the basis of the open RISC-V architecture. This command set architecture allows for the development of customer-specific special processors for safety and security an enables a high level optimization of the cores into an application.
In contrast to fully propietary solutions, these special processors are still supported by a great number of development environments and software packages (e.g. Eclipse IDE or GNU toolchain) due to the uniform command set. In addition, there can be high license fees for the use of other common controller cores (e.g. ARM-M2).
RISC-V for price-sensitive applications
Surface optimized implementations are available as base cores for price-sensitive applications in the industry. In these applications the task of the processor core is typically limited to a specific area, like regulating loops or the linearization of sensor data. These tasks can be solved cost-efficiently with a base core and a few specialized components (coprocessors or peripheral modules).
In these base cores the additional modules for cyber safety, for example secure key memory, crypto accelerators, or manipulation and firmware protection, can be integrated. Fraunhofer IMS offers adapted solutions for trustworthy hardware platforms (secure key memory).
Integrated safety and security functionality
Through the integration of monitoring functions and the redundant interpretation of critical parts of the circuit the use in fail-safe, SIL-certified systems up to SIL3 or ASIL D can be supported.
Secure key memory serves the protection of cryptographic material from manipulation or unauthorized read out. Alternatively, the key material can be extracted directly from the material properties of the manufactured chip, which is called a “Physical Unclonable Function” (PUF).