Security and key storage not only for performant systems
The individual nodes in an Industry 4.0 network form mostly small, lightweight, embedded systems. To protect embedded systems from manipulation, the system has to be identifiable and authenticate itself inside of an Industry 4.0 network. In addition, the firmware has to be stored in an encrypted form in the memory to protect it from manipulation. Also, the communication should be carried out in an encrypted way to shield the data from interception or manipulation of the data. For these tasks there are established cryptographic protocols that have been found safe that usually need a cryptographic key that is filed on the system inside of a secure key memory.
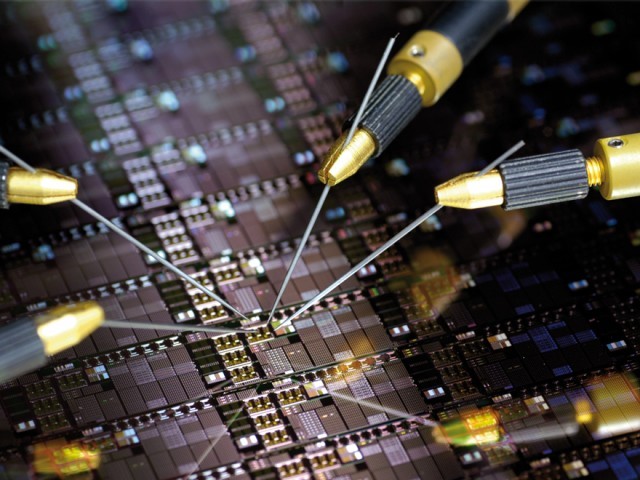
These keys are often filed in a secure storage area. For example, for smartcards or debit and credit cards an asymmetric cryptosystem is used in which the private key is generated on the device inside of a so-called hardware safety module (HSM) and filed in a memory area that cannot be read out from outside and therefore serves as a secure key memory. The key can be applied for the encryption and signing of data without leaving the system. However, such a system is not protected against hardware access to the stored key without further ado.
An individual fingerprint for every chip
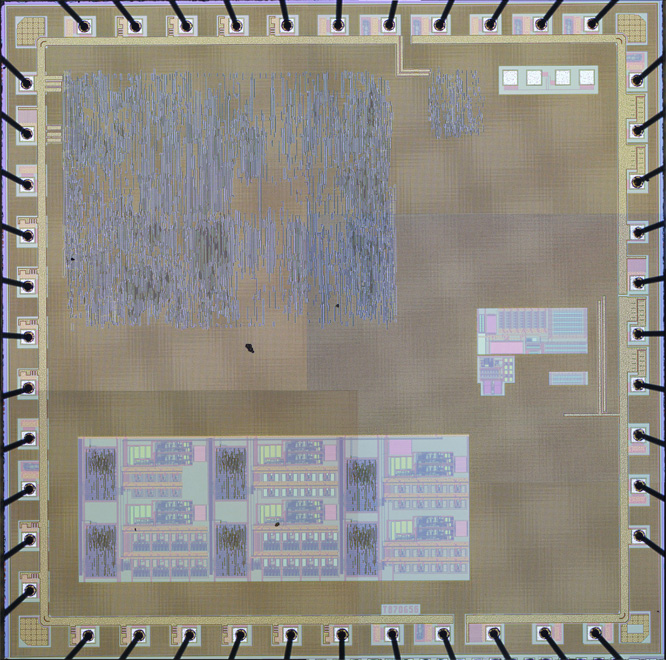
Fraunhofer IMS has developed a system that uses the random manufacturing deviations in the ASIC as an individual fingerprint to derive a cryptographic key. Every chip exhibits deviations within the defined limits of the production process, for example in the values of passive circuit elements. Combined with a robust readout circuit these elements build a secure key memory, because the saved value is undisclosed to manufacturer and user and must never leave the chip.
Because the exact value of the circuit element is generated within the production process, it can’t be recreated with another production, which is why this is called a physical unclonable element or Physical Unclonable Function (PUF). An external measurement of the small variations is practically impossible or changes the features of the component permanently and therefore realizing a high security level in comparison to common key memories. With this form of secure key memories combined with the additional manipulation safeguard, the security level can be increased even more. In the Fraunhofer-internal research project COPYCAT, for example, a manipulation protective film has been developed that safely recognizes when the electronic housing is opened and can consequently delete or block parts of the memory area. This creates an additional guard from manipulation and reverse engineering.
PUF can also be implemented as a so-called “Strong PUF”. These have with the so-called “challenge” an input word, to which the PUF sends back an individual answer or “response”. Ideally, a high number of “challenges” is available. In this way, the system can be identified, in addition to the application of a key memory, inside of a “challenge-response-protocol”, without having to carry out cryptographic calculations on the chip.
Fraunhofer IMS is currently working on a project of the cooperative industrial research (IGF), supported by the Federal Ministry of Economics and Technology (BMWi), in cooperation with the University of Applied Sciences Offenburg and a consortium of companies inside the sensor and automation industry, to make PUF technologies and secure key memories to small businesses for lightweight sensor nodes in industry 4.0 networks available.